Microsoft patches 67 vulnerabilities, including a WEBDAV zero-day actively exploited by Stealth Falcon. Critical for enterprise security.

In a monumental breakthrough, scientists have measured the speed of quantum entanglement for the first time—an achievement that is set to radically transform the way we understand the quantum world. For years, quantum entanglement was thought to be an instantaneous process, but this new research, published in Physical Review Letters, has pushed the boundaries of our knowledge, providing new insights into the quantum realm and setting the stage for revolutionary advances in data security and computational technologies.


Security teams face growing demands with more tools, more data, and higher expectations than ever. Boards approve large security budgets, yet still ask the same question: what is the business getting in return? CISOs respond with reports on controls and vulnerability counts – but executives want to understand risk in terms of financial exposure, operational impact, and avoiding loss.
The disconnect has become difficult to ignore. The average cost of a breach has reached $4.88 million, according to recent IBM data. That figure reflects not just incident response but also downtime, lost productivity, customer attrition, and the extended effort required to restore operations and trust. The fallout is rarely confined to security.
Security leaders need a model that brings those consequences into view before they surface. A Business Value Assessment (BVA) offers that model. It links exposures to cost, prioritization to return, and prevention to tangible value.

Resonantly tunable quantum cascade lasers (QCLs) are high-performance laser light sources for a wide range of spectroscopy applications in the mid-infrared (MIR) range. Their high brilliance enables minimal measurement times for more precise and efficient characterization processes and can be used, for example, in chemical and pharmaceutical industries, medicine or security technology. Until now, however, the production of QCL modules has been relatively complex and expensive.
The Fraunhofer Institute for Applied Solid State Physics IAF has therefore developed a semi-automated process that significantly simplifies the production of QCL modules with a MOEMS (micro-opto-electro-mechanical system) grating scanner in an external optical cavity (EC), making it more cost-efficient and attractive for industry. The MOEMS-EC-QCL technology was developed by Fraunhofer IAF in collaboration with the Fraunhofer Institute for Photonic Microsystems IPMS.

Notably in April, Sierra Space announced the completion of successful hypervelocity impact trials conducted at NASA’s White Sands Test Facility in Las Cruces, New Mexico, to optimize the structural integrity of Sierra Space’s LIFE habitat space station technology. This included the use of NASA’s .50 caliber two-stage light gas gun to replicate micrometeoroid and orbital debris (MMOD) impacts to LIFE’s outer shield, to prepare the space station of use in orbit.
About Sierra Space.
Sierra Space is a leading commercial space company and emerging defense tech prime that is building an end-to-end business and technology platform in space to benefit and protect life on Earth. With more than 30 years and 500 missions of space flight heritage, the company is reinventing both space transportation with Dream Chaser®, the world’s only commercial spaceplane, and the future of space destinations with the company’s expandable space station technology. Using commercial business models, the company is also delivering orbital services to commercial, DoD and national security organizations, expanding production capacity to meet the needs of constellation programs. In addition, Sierra Space builds a host of systems and subsystems across solar power, mechanics and motion control, environmental control, life support, propulsion and thermal control, offering myriad space-as-a-service solutions for the new space economy.
A joint team of researchers led by scientists at King Abdullah University of Science and Technology (KAUST) and King Abdulaziz City for Science and Technology (KACST) has reported the fastest quantum random number generator (QRNG) to date based on international benchmarks. The QRNG, which passed the required randomness tests of the National Institute of Standards and Technology, could produce random numbers at a rate nearly a thousand times faster than other QRNG.
“This is a significant leap for any industry that depends on strong data security,” said KAUST Professor Boon Ooi, who led the study, which is published in Optics Express. KAUST Professor Osman Bakr also contributed to the study.
Random number generators are critical for industries that depend on security, such as health, finance, and defense. But the random number generators currently used are vulnerable because of an intrinsic flaw in their design.
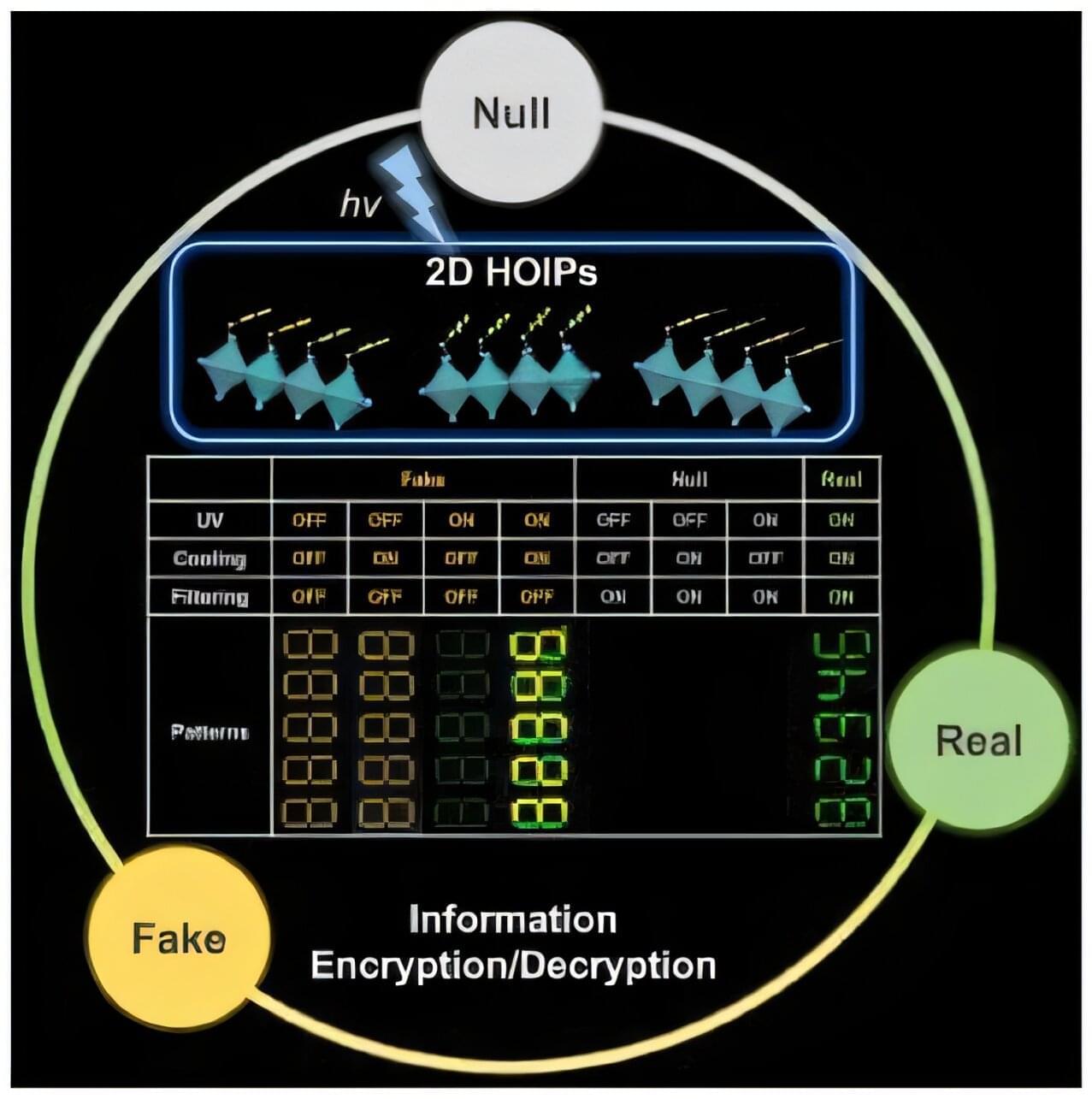
To guarantee high data security, encryption must be unbreakable while the data remains rapidly and easily readable. A novel strategy for optical encryption/decryption of information has now been introduced in the journal Angewandte Chemie by a Chinese research team. It is based on compounds with carefully modulated luminescent properties that change in response to external stimuli.
The compounds are hybrid two-dimensional organic-inorganic metal-halide perovskites, whose structure consists of inorganic layers formed from lead and iodide ions (linked PbI6 octahedra) with organic cations arranged between them. They are easy to produce, inexpensive, and printable, while demonstrating interesting optoelectronic properties.
A team led by Shenlong Jiang, Qun Zhang, and Yi Luo at the University of Science and Technology of China (Hefei) worked with three perovskites with only slight variations in their cations (phenethylammonium lead iodide perovskite (PEA)2PbI4 and its fluoridated (2-F-PEA)2PbI4 and brominated (4-Br-PEA)2PbI4 derivatives).

As many as 60 malicious npm packages have been discovered in the package registry with malicious functionality to harvest hostnames, IP addresses, DNS servers, and user directories to a Discord-controlled endpoint.
The packages, published under three different accounts, come with an install‑time script that’s triggered during npm install, Socket security researcher Kirill Boychenko said in a report published last week. The libraries have been collectively downloaded over 3,000 times.
“The script targets Windows, macOS, or Linux systems, and includes basic sandbox‑evasion checks, making every infected workstation or continuous‑integration node a potential source of valuable reconnaissance,” the software supply chain security firm said.