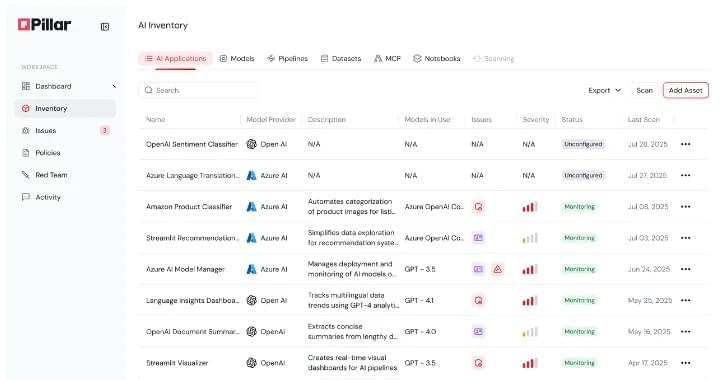
Microsoft has warned customers to mitigate a high-severity vulnerability in Exchange Server hybrid deployments that could allow attackers to escalate privileges in Exchange Online cloud environments undetected.
Exchange hybrid configurations connect on-premises Exchange servers to Exchange Online (part of Microsoft 365), allowing for seamless integration of email and calendar features between on-premises and cloud mailboxes, including shared calendars, global address lists, and mail flow.
However, in hybrid Exchange deployments, on-prem Exchange Server and Exchange Online also share the same service principal, which is a shared identity used for authentication between the two environments.