Knowing how to dispose of a printer could mean the difference between protecting personal data and letting it fall into the wrong hands.



A threat actor who claimed responsibility for the compromise of the 23AndMe site earlier this month has released a new dataset, including the records of more than 4 million people’s genetic ancestry.
The cybercriminal, known by the handle Golem, alleges in a cybercrime Dark Web forum the stolen data includes information on, “the wealthiest people living in the US and Western Europe,” according to reports.
23andMe spokesperson Andy Kill said in a statement the organization is still trying to confirm whether the most recently leaked data is genuine.
If you wanted to, you could access an “evil” version of OpenAI’s ChatGPT today—though it’s going to cost you. It also might not necessarily be legal depending on where you live.
However, getting access is a bit tricky. You’ll have to find the right web forums with the right users. One of those users might have a post marketing a private and powerful large language model (LLM). You’ll connect with them on an encrypted messaging service like Telegram where they’ll ask you for a few hundred dollars in cryptocurrency in exchange for the LLM.
Once you have access to it, though, you’ll be able to use it for all the things that ChatGPT or Google’s Bard prohibits you from doing: have conversations about any illicit or ethically dubious topic under the sun, learn how to cook meth or create pipe bombs, or even use it to fuel a cybercriminal enterprise by way of phishing schemes.

State-sponsored threat actors from Russia and China continue to throttle the remote code execution (RCE) WinRAR vulnerability in unpatched systems to deliver malware to targets.
Researchers at Google’s Threat Analysis Group (TAG) have been tracking attacks in recent weeks that exploit CVE-2023–38831 to deliver infostealers and backdoor malware, particularly to organizations in Ukraine and Papua New Guinea. The flaw is a known and patched vulnerability in RarLab’s popular WinRAR file archiver tool for Windows, but systems that haven’t been updated remain vulnerable.
“TAG has observed government-backed actors from a number of countries exploiting the WinRAR vulnerability as part of their operations,” Kate Morgan from Google TAG wrote in a blog post.
🕵️♂️ Nation-state hackers are turning to Discord. Discover how they’re using this social platform for potential cyber-espionage and target critical infrastructure.
Read:
In what’s the latest evolution of threat actors abusing legitimate infrastructure for nefarious ends, new findings show that nation-state hacking groups have entered the fray in leveraging the social platform for targeting critical infrastructure.
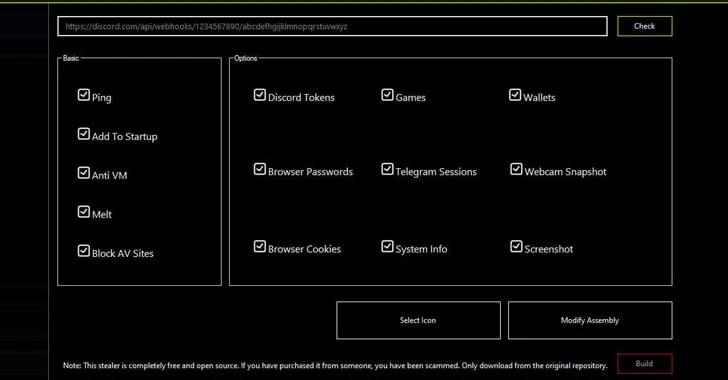
Discord, in recent years, has become a lucrative target, acting as a fertile ground for hosting malware using its content delivery network (CDN) as well as allowing information stealers to siphon sensitive data off the app and facilitating data exfiltration by means of webhooks.
“The usage of Discord is largely limited to information stealers and grabbers that anyone can buy or download from the Internet,” Trellix researchers Ernesto Fernández Provecho and David Pastor Sanz said in a Monday report.
Zero-day alert: 10K cisco IOS XE systems now compromised:
Just a day after Cisco disclosed CVE-2023–20198, it remains unpatched, and one vendor says a Shodan scan shows at least 10,000 Cisco devices with an implant for arbitrary code execution on them. The vendor meanwhile has updated the advisory with more mitigation steps.

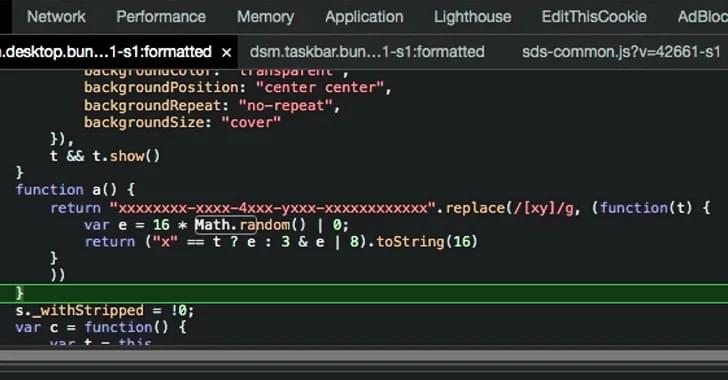
‘Etherhiding’ Blockchain Technique Hides Malicious Code in WordPress Sites: https://informatech.co/3S3tw
A threat actor has been abusing proprietary blockchain technology to hide malicious code in a campaign that uses fake browser updates to spread various malware, including the infostealers RedLine, Amadey, and Lumma.
While abuse of blockchain is typically seen in attacks aimed at stealing cryptocurrency — as the security technology is best known for protecting these transactions — EtherHiding demonstrates how attackers can leverage it for other types of malicious activity.
Researchers from Guardio have been tracking a campaign dubbed ClearFake over the last two months in which users are misled into downloading malicious fake browser updates from at least 30 highjacked WordPress sites.

After sifting through more than 1.8 million pages identified as admin portals, researchers made a disheartening discovery — 40,000 of them used “admin” as its password, making it the most popular credential used by IT administrators.
The research was conducted on 2023 passwords between January and September by a team with Outpost24, which also found an increased reliance on default passwords.
The top 10 passwords discovered by the analysis included common defaults and easy-to-guess options: