“This isn’t just an investment — it’s a clarion call for Charlotte to be the ‘Silicon Valley of the South,’” a local cybersecurity expert said of Amazon’s $10 billion plans.



It’s worth noting that similar social engineering tactics have been employed by threat actors associated with the Black Basta ransomware operation.
“Victims are carefully targeted and persuaded to execute a script that triggers the download of an archive,” Morphisec CTO Michael Gorelik said. “This archive contains a renamed Notepad++ updater (GUP), a slightly modified configuration XML file, and a malicious side-loaded DLL representing the Matanbuchus loader.”
Matanbuchus 3.0 has been advertised publicly for a monthly price of $10,000 for the HTTPS version and $15,000 for the DNS version.
This message will self-destruct in 3… 2… 1 is something you’ve definitely seen in Mission: Impossible films over the years.
Now, we finally have tech that feels just as futuristic, thanks to a new kind of storage hardware.
Taiwanese company TeamGroup has unveiled a new internal SSD that can literally destroy itself at the press of a button, ensuring sensitive data never falls into the wrong hands.
The device, called the P250Q-M80, is aimed at sectors where top-tier data security isn’t just a perk, it’s a necessity. We’re talking defense, industrial automation, AI development, and maybe even the crypto wallet you hold.
TeamGroup showcased the drive at Computex 2025, where it took home a Best Choice Award in the cybersecurity category.

Cloudflare on Tuesday said it mitigated 7.3 million distributed denial-of-service (DDoS) attacks in the second quarter of 2025, a significant drop from 20.5 million DDoS attacks it fended off the previous quarter.
“Overall, in Q2 2025, hyper-volumetric DDoS attacks skyrocketed,” Omer Yoachimik and Jorge Pacheco said. “Cloudflare blocked over 6,500 hyper-volumetric DDoS attacks, an average of 71 per day.”
In Q1 2025, the company said an 18-day sustained campaign against its own and other critical infrastructure protected by Cloudflare was responsible for 13.5 million of the attacks observed during the time period. Cumulatively, Cloudflare has blocked nearly 28 million DDoS attacks, surpassing the number of attacks it mitigated in all of 2024.


An international law enforcement action dismantled a Romanian ransomware gang known as ‘Diskstation,’ which encrypted the systems of several companies in the Lombardy region, paralyzing their businesses.
The law enforcement operation codenamed ‘Operation Elicius’ was coordinated by Europol and also involved police forces in France and Romania.
Diskstation is a ransomware operation that targets Synology Network-Attached Storage (NAS) devices, which are commonly used by companies for centralized file storage and sharing, data backup and recovery, and general content hosting.

A new variant of the Konfety Android malware emerged with a malformed ZIP structure along with other obfuscation methods that allow it to evade analysis and detection.
Konfety poses as a legitimate app, mimicking innocuous products available on Google Play, but features none of the promised functionality.
The capabilities of the malware include redirecting users to malicious sites, pushing unwanted app installs, and fake browser notifications.

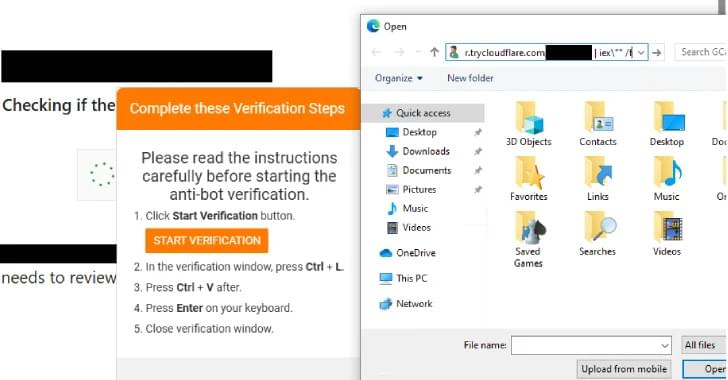
Threat actors behind the Interlock ransomware group have unleashed a new PHP variant of its bespoke remote access trojan (RAT) as part of a widespread campaign using a variant of ClickFix called FileFix.
“Since May 2025, activity related to the Interlock RAT has been observed in connection with the LandUpdate808 (aka KongTuke) web-inject threat clusters,” The DFIR Report said in a technical analysis published today in collaboration with Proofpoint.
“The campaign begins with compromised websites injected with a single-line script hidden in the page’s HTML, often unbeknownst to site owners or visitors.”